Why Your AI Needs a Consent Graph
Why Your AI Needs a Consent Graph
October 13, 2025
Your AI Marketing Stack Needs Permission, Not Vibes
Personalization and AI agents are the candy everyone wants, but the real foundation is not ChatGPT rewriting your newsletter overnight. It is permission, specifically machine-readable, auditable permission that runs underneath the stack. Slapdash checkboxes and five-tool form fields do not scale. If your growth now hinges on automations that write, schedule, answer, route, and publish without human in the loop, you need a consent graph.
What is a consent graph? Think of it as the operating system for who you can talk to, how you can talk to them, about what topics, with which evidence, and for how long. With new inbox rules cracking down and answer engines like ChatGPT search using your content in ways you may never see, first-party trust is the only defensible edge. A consent graph is the compliance and trust layer that lets your automations move at machine speed without lighting your reputation on fire.
What a Consent Graph Actually Is
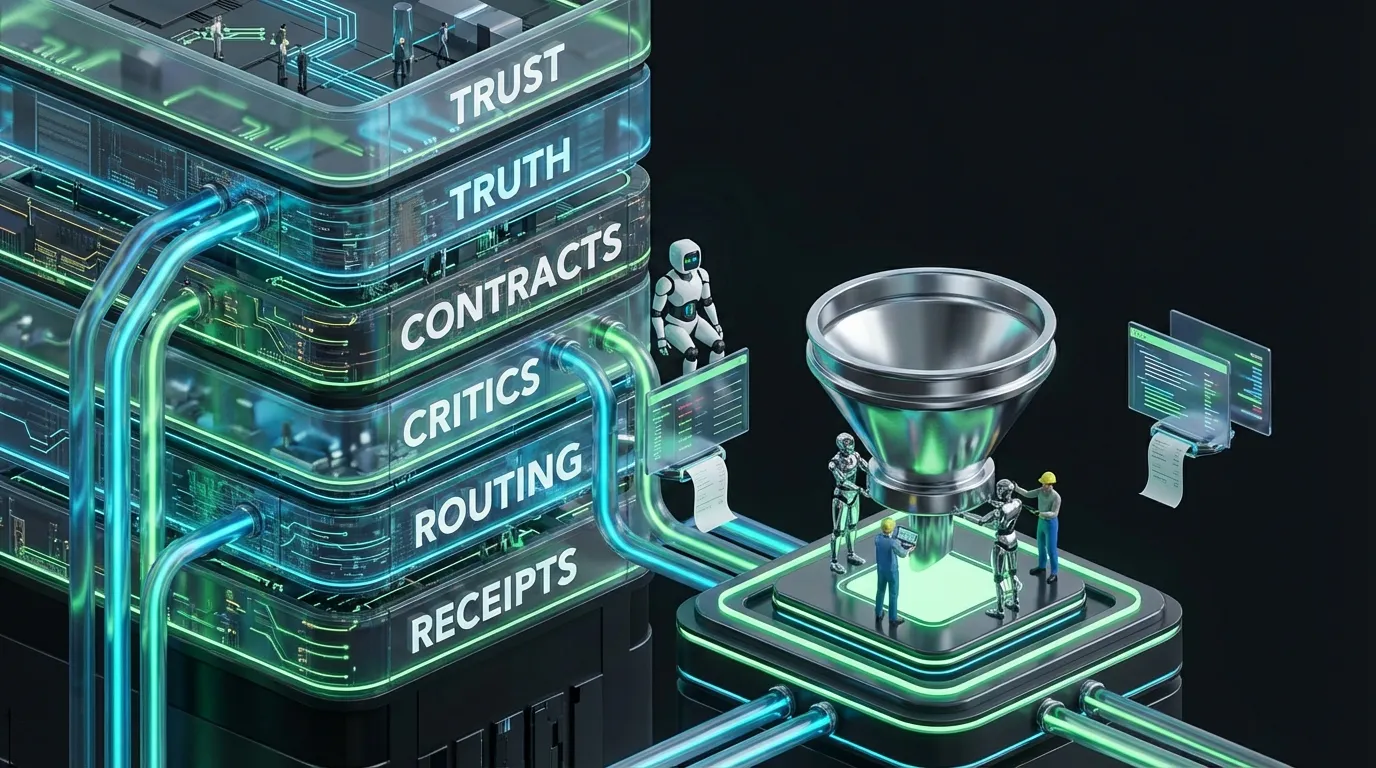
Forget the “opt-in” checkbox crammed in your CRM. A proper consent graph is a structured, queryable map of identities, channels, purposes, and the legal or policy basis that glues them together. Every entry points back to evidence (not vibes!), expiration, and audit history. Every action your automation stack takes should reference the exact consent node authorizing it.
- Identity: The person or entity, resolved across email, phone, device, social, and work accounts.
- Channel: Email, SMS, push, DM, ads, phone calls, IRL booth scans, if you can message there, it is a channel.
- Purpose: What you are doing, newsletters, updates, onboarding help, promos, surveys.
- Basis: The legal or policy reason you can use their data.
- Scope and region: Where the permission applies and under what limitations.
- Evidence: Timestamps, source data, receipts, file links, maybe a reviewer.
- Status: Active, revoked, expired, or contested, never static and never deleted.
Why This Matters Now
- Inbox rules just got teeth: Sending authenticated mail and honoring unsubscribes is no longer best practice. It is table stakes. AI-generated drivel is not why your stuff lands in spam. Ignoring permission flows is.
- Cookies’ days of magic are waning: Third-party cookies still exist, but users dictate terms now. Relying on patchworked identity hacks will not save you. First-party trust beats tracking tricks.
- Answer engines and assistants changed the content game: Generative search prioritizes clean attribution. Claims without clear provenance invite lawsuits and brand headaches.
Anatomy of a Consent Graph
| Entity | Examples | Key Fields | Operational Notes |
|---|---|---|---|
| Identity | Email, phone, device ID, workspace handle | resolved_id, merge_history, confidence | Use deterministic rules before probabilistic lookups |
| Permission | Newsletter, product update, promo, survey | purpose, basis, scope, region | Every campaign needs a mapped, valid purpose |
| Channel | Email, SMS, push, DM, booth capture | channel_type, provider, auth_status | Track per-channel engagement and compliance |
| Evidence | Form intake, QR sign-up, waivers, call transcripts | timestamp, source, asset_ref, checksum | Proof must be retrievable in a click, no exceptions |
| Status | Active, revoked, expired, contested | state, changed_at, changed_by | Keep immutable history for every change |
Minimal JSON Schema to Get Started
{
"identity": {
"resolved_id": "u_7f3a1",
"emails": [
{ "address": "ana@brand.com", "verified": true, "primary": true }
],
"phone": [{ "number": "+14155550123", "verified": false }],
"handles": [{ "platform": "linkedin", "id": "ana-mktg" }]
},
"permissions": [
{
"purpose": "newsletter",
"channel": "email",
"basis": "consent",
"scope": ["global"],
"region": ["US"],
"evidence": {
"timestamp": "2024-11-07T15:31:22Z",
"source": "landing_form",
"asset_ref": "s3://consent/forms/ana_1130.pdf",
"checksum": "sha256:...",
"reviewer": null
},
"status": { "state": "active", "changed_at": "2024-11-07T15:31:22Z" },
"expires_at": null
}
],
"channel_settings": {
"email": { "spf": true, "dkim": true, "dmarc": "p=none" },
"sms": { "brand_registered": true }
}
}
Keep it simple, make it explicit, and ensure your automations can query and reference every action.
How a Consent Graph Supercharges Your Automation
- Email deliverability: Outbound checks consent and purpose before queuing. No valid node equals no send. Result: fewer spam complaints and a stronger sender reputation.
- Audience building: Suppression lists feed off revoked or expired entries. Lookalike seeding uses only active, scoped permissions.
- Personalization gates: AI only queries first-party data if current permission allows. Sensitive content defaults to generic if consent lapses.
- Agent constraints: Agents can read identity, but must fetch permission tokens for outreach. Tokens expire, sensitive actions escalate to humans.
- Attribution sanity: Consent bound to identity means you can credibly track conversions without dancing near privacy violations or hypothetical journeys.
What Changed in Deliverability and Why Permission Fixes It
Inbox providers want authentication (SPF, DKIM, DMARC), one-click unsubscribes, and low complaints. Ignore these, and your emails will land in the void. The must-have playbook:
- Authenticate each domain with SPF and DKIM, and publish a DMARC policy that means business.
- Implement one-click unsubscribe and process requests within two days.
- Monitor campaign and list-level complaints. Investigate any spike.
- Throttle by observed channel health. Scale only as reputation heals.
- Separate transactional and promotional emails across different sending domains, each with clear purpose tags.
A consent graph enforces these rules as code, not wishful thinking. Automations do not improvise. They ask the graph.
Cookies Survived, but Should Not Drive Your Strategy
Third-party cookies are in hospice care, not dead, but user visibility and control keep rising. Platforms push for privacy-forward APIs. First-party trust, cemented by your consent graph, gives you flexibility, you can retarget by cookie where ethical, but your main identity and permission state do not depend on a brittle mesh of anonymous IDs. Your AI runs on relationships you can actually prove.
Answer Engines Reward Structured Consent and Provenance
GenAI answer engines and assistants surface content with clear sourcing and verifiable authority. If your consent and content governance both live in the same graph, you can feed answer engines true, up-to-date information and avoid wild hallucinations quoted by prospects, partners, or bots on your next review call.
IRL Is Back. So are Waivers, QR, and Structured Proof.
Live activations are back in fashion. But they are notorious for creating chaos unless intake is structured from the start. The fix:
- QR codes linked to venue-specific, purpose-limited forms in every locale you activate.
- Photo, video, and live voice consent auto-attached to the person’s graph node.
- Route every intake through a policy pack. If consent lacks scope or evidence, suppress that asset in every system.
- Post-event emails with one-click unsubscribe option pre-wired. Trust is built in, not glued on.
Your consent graph becomes your in-person and online bridge. No more guesswork about what is allowed where.
Consent Graph Blueprint: Components, Impact, and Core Metrics
| Component | What It Unlocks | Risk Reduced | Core Metric |
|---|---|---|---|
| Identity resolution | Omni-channel targeting and suppression | Duplicate sends, complaint bursts | Matches, dedupes |
| Purpose-bound consent | Personalization, compliant outreach | Policy breaches, spam complaints | Complaint rates, coverage |
| Evidence register | Instant audits, self-serve proof | Legal exposure, endless investigations | Proof retrieval speed |
| Channel health | Adaptive throttling and rerouting | Reputation loss, blocklisting | Inbox and rate limits |
| Policy packs | Enforceable, consistent rules | Ad hoc mistakes, selective enforcement | Policy pass or fail |
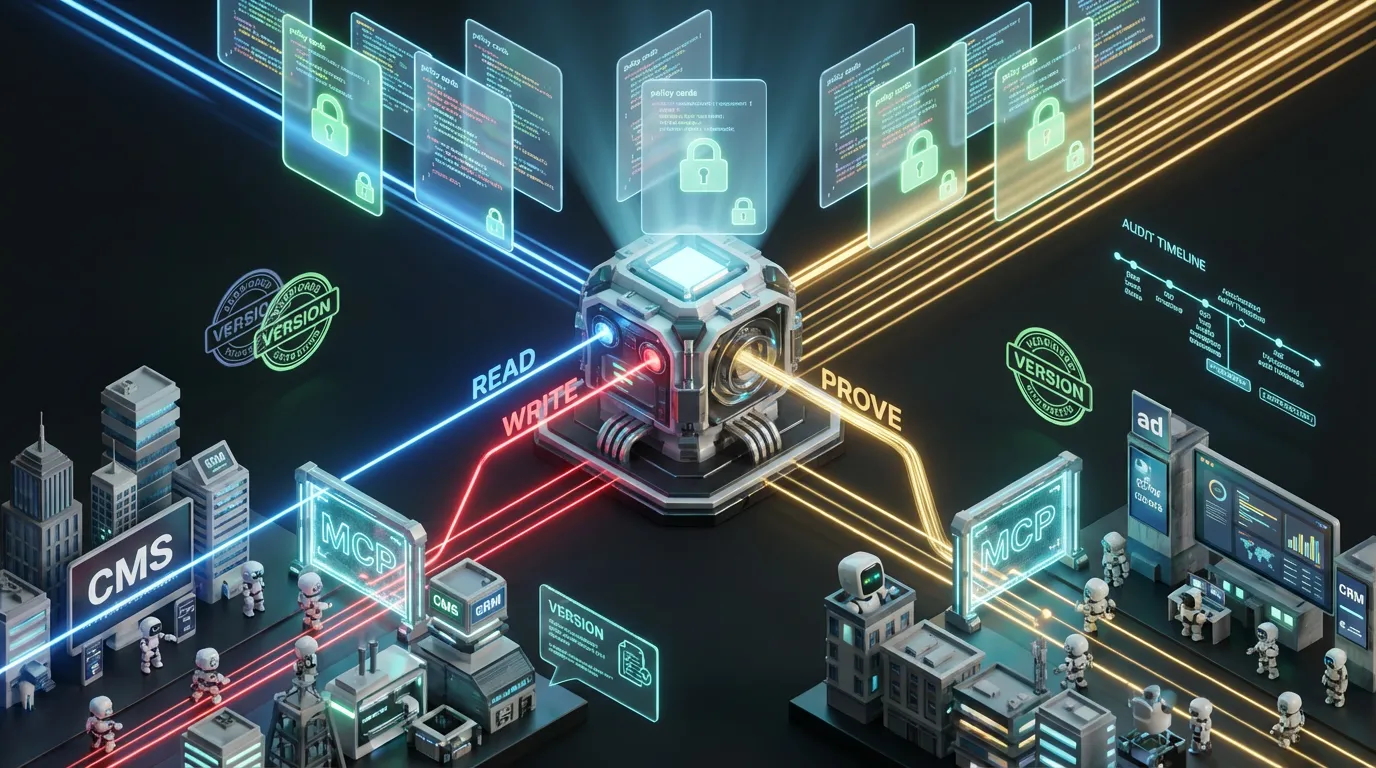
Build It With What You Already Own
No need for a seven-figure MarTech explosion. Start with a few explicit tables or docs and graduate from good enough to scale-proof as you grow:
- Data spine: Start with a spreadsheet or Notion DB covering identities, permission state, evidence, and status.
- Capture: Use form tools that require a purpose field and allow evidence uploads. Event forms can be QR-ified, localized, and short.
- Automation: Mandate that your orchestration stack queries the consent database before any send, write, or publish.
- Proof store: Cloud storage for immutable assets and checksums, chained to your main record.
- Authentication: Monitor DMARC, SPF, and DKIM daily. Do not ride blind.
When volume spikes, move the schema into a database and layer on an API for agents and workflow tools. The permission logic stays the same.
Operational Guardrails, Rules That Actually Work
- Never send to an identity unless permission is active, scoped, and covers the action and channel.
- Process unsubscribes instantly and append proof to the user’s consent record.
- Log proof and a minimal reason with every outbound action.
- Segment trial, prospect, and customer comms by purpose. Never mix.
- Set service-level thresholds for bounces, complaints, and spikes to trigger auto-suppression and human review.
AI Agents: Fast, Diligent, and Permission-Aware
Agents that crank out work are great. So are the ones that confidently blast emails to fifth cousins with no authorization. Avoid that fate. Let your agents play by the graph:
- Agents must request permission tokens. Tokens encode channel, purpose, and time to live.
- No token? Agents draft but do not send or publish.
- Tasks above a certain risk auto-require a human click, with all proof up front.
- Nobody announces price changes or legal moves with agent-only workflows. Always escalate.
Boring? Maybe. But this boring is what delivers speed, control, and audit trails in the real world.
Phased Rollout Plan
Phase One: Make Permission Explicit
- Select a pilot channel. Define the schema, and tag the evidence you actually intend to keep.
- Set your sender tools to block anything without an active, matching permission.
- Log all unsubscribes to the same consent record. Confirm opt-out back to the contact.
Phase Two: Layer Channel Health and Proof
- Enforce SPF, DKIM, and DMARC everywhere. Track daily.
- Attach receipts and checksums to every new consent entry. Benchmark retrieval speed.
- Throttle volumes based on observed sender health. Do not outpace your reputation.
Phase Three: Ramp Up on Scope and Agents
- Add SMS, push, and DMs. Copy the same guardrails.
- Switch agents to work through a permissions API. Issue tokens, and escalate on edge cases.
- Deploy policy packs for sensitive use cases, and cordon high-impact flows behind human review.
Metrics That Matter
- Consent coverage: Share of your audience with valid, scoped permissions for each campaign type.
- Complaint rate: Tracked by sender, campaign, and list.
- Inbox rate: Deliverability sliced by segment and channel.
- Unsubscribe latency: Time from click to global suppression.
- Proof retrieval time: Seconds required to bring up audit evidence.
- Agent override rate: How often humans intercept or modify agent actions.
Top Failure Modes and the Fix
- Check-box consent: Replace binary fields with detailed, purpose- and evidence-linked permission records.
- Identity confusion: Merge on strong signals and keep a reversal trail.
- Policy theater: PDFs and docs do not enforce themselves. Encode them as checks that run before sends.
- Agent feedback loops: Cap retries and token lifetimes. Low confidence always escalates.
- Invisible drift: Set up real-time monitoring for spikes in complaints, bounces, or proof failures.
SMB and Creator Edition
- Get started with one spreadsheet. Key columns: email or handle, purpose, channel, evidence_link, status, last_changed.
- Archive screenshots or PDFs of each consent form or checkout in a single folder.
- Build your automations to check this sheet before any send or publish.
- Keep a tab to log sender health, SPF, DKIM, and DMARC status, updated weekly.
- Make unsubscribing instant, visible, transparent, and logged. Deliverability is your moat.
How the Consent Graph Moves the Bottom Line
- More inbox placement, more sends, and a longer sender lifespan. This means more sales and less churn.
- No more frantic hotfixes after an “oops” blast or careless campaign.
- Personalization stays compliant and on-brand, no privacy trip wires.
- Agents move fast, and the brakes work when it matters.
- Proof is always on tap for platform audits, partners, and regulators. No sweaty discovery calls.
Executive Checklist
- Do you have a unified, queryable consent log tied to purpose and evidence?
- SPF, DKIM, and DMARC: Are they configured and monitored, everywhere you send?
- Is one-click unsubscribe live with low-latency suppression, and is it measured?
- Can proof of consent be found in under a minute for any record?
- Are your AI agents required to fetch permission tokens and escalate when uncertain?
- How many of your policies are enforced as executable checks, and are you tracking that pass rate?
The Take
Automation-first teams do not move fast and break things. They move fast because their automation stack knows the rules, checks the facts, and ships with receipts. A consent graph is not flashy, but it unlocks reputation, compliance, and leverage that manual teams cannot touch. Build it, wire it everywhere, and prove trust at scale. This is how you future-proof the AI-powered stack. No vibes required.
Further reading on inbox controls: Gmail’s recent Manage Subscriptions experience makes unsubscribing easier, which raises the bar for permission hygiene.