Provenance Pipelines Supercharge AI Marketing
Provenance Pipelines Supercharge AI Marketing
November 29, 2025
Welcome to 2025, the year marketers finally realized the provenance of their AI content is not just a bullet point for compliance reports. Now it is also the secret handshake to faster shipping, higher margins, and fewer “Hey, is that even legit?” emails from regulators and marketplace partners. If you want your content front and center on discoverable, monetizable platforms, it pays to have a paper trail (or in this case, a cryptographically signed digital authenticity passport). Provenance is your new growth lever. Treating it as a first-class citizen in your automation stack will not just keep you out of headline-making scandals: it will get you picked by AI assistants, overview modules, and procurement bots that decide who gets seen and sold.
If you want to ship compliant assets at scale with Llama 4, GPT-5, Gemini Ultra, or any of the other heavy hitters, this is how modern provenance actually works, why it matters now, and how to wire up pipelines that sign, verify, and measure content proof across text, image, video, and any claims you make. No buzzword bingo, no drama, just receipts.
What Even Is Provenance? Breaking Down the Buzzwords
Let’s keep the hype to a minimum. You’ll run into three classes of “proof” systems, and you probably need to stitch two of them into your workflow, minimum:
| Technique | What it does | Best for | Weak spots |
|---|---|---|---|
| Invisible watermarking | Embeds a persistent, typically machine-detectable signal in media | Platform attribution and automated detection | Breaks during heavy edits; cannot stand alone as proof for audits |
| Content credentials (C2PA or similar) | Adds tamper-evident metadata, such as authorship, edit history, and tool chain | Platform trust, commercial partners, publisher compliance | Prone to metadata stripping without enforced validation |
| Operational receipts | Logs and stores generation steps, reviews, costs, and approvals in internal systems | Finance, legal, and shared-vendor audits | Not portable; needs a summary or link attached to asset exports |
Translation: Watermarks = handshake, credentials = passport, receipts = tax returns. Distribution requires at least credentials; defensibility also needs receipts.
Why Now? The Tipping Point For Provenance
- Platforms demand verifiability: AI tagging and content credentials are now the price of entry for better search, recommendations, and ad placements. If you cannot prove who made it, some algorithm will quietly push it down the stack.
- Marketing automation finally grew up: Digital asset managers and content routers now blend AI tagging with credential checks, making compliance just part of getting content live.
- Regulators and marketplaces got teeth: Rights, sources, and disclosures are now actively policed, often automatically. Expect door-slamming if your claims cannot be sourced or rights are expired.
- AI assistants act as gatekeepers: Large platforms and on-site bots increasingly “prefer” content that brings receipts: signed objects with structured, verified claims embedded.
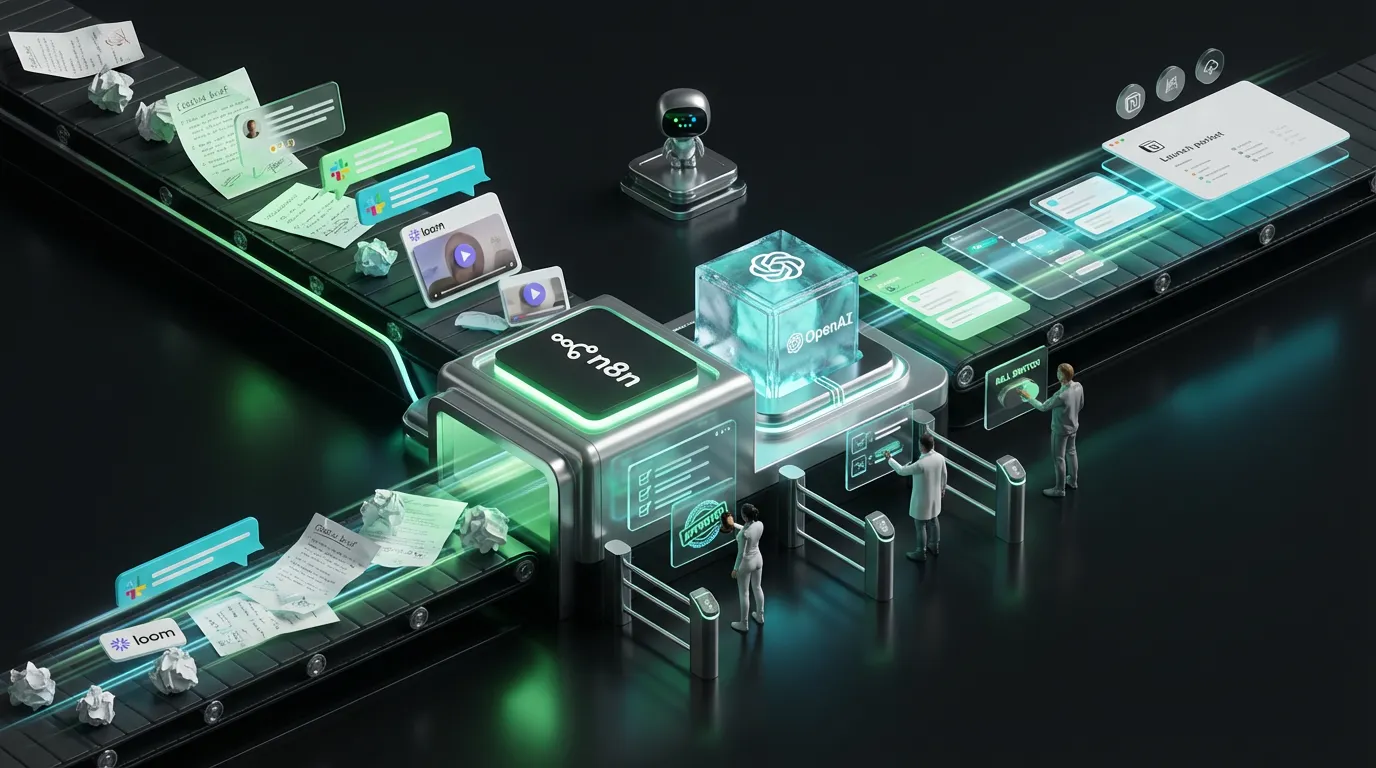
Provenance Pipeline Anatomy, End to End
[Truth] → product specs • pricing • claims, each with a source ID • rights & eligibility [Generate] → draft text, images, video snippets (bonus: output as structured objects, not blobs) [Sign] → stamp credentials: author, tools, sources, rights, locale [Critic] → run automated schema, claim, locale, rights, and cost checks [Publish] → hand-off to CMS / ad platform / social queue / assistants [Observe] → track coverage, credential retention, cost per compliant asset, and defect escapes
Credential Ingredients: What Actually Belongs Inside
A content credential is a signed, minimally invasive, portable proof—visible to machines, readable by humans, and persistent through common edits.
{
"credential": {
"asset_id": "vid_057C",
"type": "ai_short_video",
"authors": ["creator:@mina", "brand:acme"],
"tools": ["image_model:llama4-vision", "video_editor:gemiUltraClip"],
"sources": [
{"claim": "99.95% uptime", "source_id": "q2_2025_opsreport"},
{"claim": "Installs in 72 hours", "source_id": "slate_ops_q2"}
],
"rights": {"territories": ["US", "EU"], "usage": ["ads", "owned_social"], "expiry": "2027-01-01"},
"locale": "en-US",
"disclosure": ["Brand partnership"],
"hash": "sha256:...",
"signature": "ed25519:..."
}
}
No rogue data, no mystery fields—just identity, source, rights, and a real signature.
Receipts: The CFO’s Favorite Part
Credentials answer questions for platforms and partners. Receipts answer the ones your C-suite cares about—budget, process, and risk.
{
"receipt": {
"asset_id": "vid_057C",
"route": ["llama4_text", "gemiUltraClip"],
"input_tokens": 1620,
"output_tokens": 350,
"retries": 1,
"human_minutes": 5.2,
"cost_usd": 0.89,
"critics": {"schema": "pass", "claims": "pass", "rights": "pass", "accessibility": "pass"},
"decision": "publish"
}
}
Together, credentials and receipts build scalable, auditable, defendable automation pipelines.
No-Code & Low-Code Plug-Ins For Provenance
- Digital Asset Managers (DAM) & Media Asset Managers (MAM): Trigger credential signing at ingest and publish. If credentials are missing or broken, block export automatically.
- CMS and Social Schedulers: Drop in a badge—green if all fields (esp. rights and disclosure) are valid; red with a fix-list otherwise.
- Ad Ops: Check region locks, usage rights, and campaign target match before anything hits “live.”
- Conversational Assistants and Answer Surfaces: Bundle credentials with response snippets. If a user or downstream service asks for proof, your objects are already signed and ready.
Policy As Code: Automating More Than Structure
Most marketing teams already use code to enforce schema and cost rules. Add provenance to your critic chain and make policy drift a thing of the past.
{
"critics": {
"schema": {"enforce": true, "schema_id": "Asset2025Q4"},
"claims": {"numeric_require_source": true, "allowed_sources": ["q2_2025_opsreport", "slate_ops_q2"]},
"rights": {"territory_lock": true, "expire_on": true},
"disclosure": {"require": ["Brand partnership", "#ad"]},
"locale": {"region": "EU", "currency": "EUR"},
"accessibility": {"captions": true, "alt_text": true},
"cost": {"max_cost_usd": 1.00, "retry_limit": 2}
}
}
Critical: Block on missing sources, expired rights, or broken disclosure. Allow exactly one auto-repair, but escalate after that.
Failure Modes: How Good Pipelines Really Break
| Failure | Root Cause | Fast Fix |
|---|---|---|
| Credentials lost on export | Transcoding/optimization step fails to preserve metadata | Enforce credential-aware export presets, and always run post-export validation |
| Mismatched or out-of-date claims | Overly manual copywriting; unversioned claims database | Require source IDs, invalidate content when “truth pack” version changes |
| Expired rights | No automated kill switch tied to end-dates | Add a global rights gate. If the date hits, block scheduling & ads |
| Locale mismatch in captions | Automated translate steps ignore locale critic | Enforce locale via critic; spot-check risky assets |
| Cost overruns in agent-driven loops | No cap on retries or escalation | Lock max cost per asset, bias toward the smallest (cheapest) model first |
Metrics To Track In a Provenance-Obsessed World
- Credential Coverage Rate: Percentage of assets shipped with signed, valid credentials.
- Credential Retention Rate: Percentage of assets whose credentials survive edits, exports, or platform hops.
- Inclusion Uplift: Uptick in AI assistant or recommender inclusion after credential rollout.
- Cost Per Compliant Asset: All-in cost per credentialed, compliant piece of content.
- Defect Escapes: Number of assets published with missing or broken credentials, per thousand shipped.
Structured Answers: Verifiable Content For The Age of Assistants
AI surfaces do not want essays. They want answer cards with verifiable claims, signatures, and tight eligibility. Here’s a pattern:
{
"answer_card": {
"id": "router_pro_2025",
"intent": "compare_and_buy",
"summary": "Tri-band Wi-Fi 7, independently verified performance.",
"claims": [
{"text": "Up to 980 Mbps (lab test Q2 2025)", "source_id": "lab_ops_q2"},
{"text": "Average setup: 69 hours", "source_id": "slate_ops_q2"}
],
"eligibility": {"regions": ["US-MA", "US-CA"]},
"next_actions": ["check_inventory", "start_checkout"]
},
"credential": {"signature": "ed25519:...", "hash": "sha256:..."}
}
Keep these cards and their credentials glued together. That way, anyone (or any system) down the supply chain can instantly verify the facts and rights.
Provenance Playbooks By Org Size
Creators & Micro Brands
- Enable content credentials for every image and video. Minimal required fields: author, tool, rights, and disclosure.
- Auto-block on missing fields; run weekly credential coverage reports.
- Fix your worst pipeline offender every week until coverage stabilizes.
Mid-Market Teams
- Centralize all product “truths” with versioned source IDs; enforce these for all claims.
- Require credential signing at ingest and publish; run a check after every major edit or format hop.
- Cap model use by default (start with smallest/cheapest), only escalate defaults when critic chain calls for bigger guns.
Enterprise & Regulated Orgs
- Default to region-locked rights and per-asset disclosures; automatically block outbound boosts beyond contract territory.
- Export an audit-ready receipt (with hash) for every asset shared downstream.
- Run monthly credential-retention regression and “defect escape” analysis; tie global kill switches to any policy drift events.
Getting Provenance Live: Your First 30 Days
Week 1: Audit & Schema Build
- Map high-volume asset flows and key channels. Create tight credential schemas for each asset type.
- List and enforce all required credential fields (author, tools, claim source, rights, locale, disclosure).
Week 2: Critics and Signing Deploy
- Deploy credential signing in your asset manager or pipeline. Validate both at ingest and before publish.
- Stand up critics for every filter—schema, claim, rights, locale, accessibility, and cost. Allow a single repair, then escalate.
Week 3: Shadow Mode, Then Canary
- Run provenance checks silently in parallel. Log credential strip rates and common failures without blocking yet.
- Promote a “canary” group of assets to full credential enforcement with rollback ready.
Week 4: Publish With Metrics
- Report actual coverage, retention, defect escapes, and compliant-asset cost. Iterate and scale to second channels once stable.
Structure Governance So It Actually Makes You Faster
- Risk tiers: Low-risk assets auto-publish once critics pass; pricing, benchmarks, and comparisons get routed to a human; highly regulated content goes straight to legal for final review.
- Receipts, or it did not happen: Every asset logs its route, cost, and reviewers for automated audit trails.
- Global kill switches: If credential strip rates spike, or a major policy change is triggered, freeze that pipeline instantly with no “oops, I thought someone else had it covered” moments.
Sanity Checks Before You Crown the Automation King
- Automation is not free: Every retry and escalation burns cash. Set hard retry and escalation caps—especially as large model calls get pricier.
- Humans still have a job: Use machines for proofs, approvals, and logistics. Keep humans for risk, novelty, taste, and edge-case coverage.
- Benchmarks only hint at value: Your actual inclusion rate, credential coverage, and defect escapes are what move the needle—not how you rank on some leaderboard.
The COEY Take
Want AI-powered growth without the drama? Provenance is your insurance, your platform accelerant, and your shield against chaos. Ship every asset with a signed digital passport, source-verified claims, and rights/disclosure baked right in. Automate as far as you safely can, send receipts up the chain, and escalate only when the facts demand a bigger, slower model. Block anything that cannot prove itself, and suddenly your marketing pipeline is not just compliant, it’s unkillable, discoverable, and very hard to outmaneuver.