Provenance-First Automation for AI Marketers
Provenance-First Automation for AI Marketers
December 5, 2025
The generative floodgates are open again. Your new agency of AI assistants can spin up a dozen campaign assets before you finish your coffee. But unless your content can prove where it came from and what it is allowed to do, those beautiful renders and punchy sales claims will tank your trust score with both platforms and people. Provenance-first automation is not a nice-to-have. It is now the price of entry.
The difference today is simple. The provenance layer is no longer a bolt-on for high-speed content engines. It is packageable, cryptographically provable, and increasingly built into products you already use. Open standards such as Content Credentials (C2PA) and modern media platforms are making verifiable asset histories normal rather than exotic. When proof travels with every file, assistants prefer you, platforms relax, and your automations stop second-guessing themselves.
Provenance for Marketers: What It Actually Means
Provenance, in the post‑AI production era, is the unbroken origin story of your asset, signed, timestamped, and attached as data. For modern marketing operations, that means rolling up:
- Content Credentials: Signed, portable manifests declaring author, edits, tools, and policy assertions.
- Watermarking: Robust, machine-readable signals that survive file conversions and reposting at scale. See Google DeepMind’s SynthID.
- Receipts: Immutable ledgers for each asset, tracing model routes, human approvals, and cost.
- Rights and Disclosures: Usage windows, territories, creator approvals, and legal notices as first-class, machine-enforceable fields.
| Layer | Solves | Weak spot |
|---|---|---|
| Content Credentials | Origin, edit history, toolchain transparency | Strippable unless cryptographically bound |
| Watermarking | Media-scale authenticity | Signal can degrade under aggressive transforms |
| Receipts | Audit trails, cost tracking, regression testing | Only work when enforced pre-publish |
| Rights & Disclosures | Legal safety, platform compliance | Worthless if disconnected from enforcement |
Why This Shifted From “Nice” to Non‑Negotiable
- Assistants and platforms are favoring verifiable assets: Major vendors have moved to open standards and programs for content authenticity. For example, OpenAI joined the C2PA steering committee in 2025, reflecting a broader trend toward provenance-aware ecosystems. Details.
- Tooling rewards transparency: Capture and editing apps are adding built-in credentials and watermarks, and open standards such as C2PA keep improving portability and robustness.
- AI‑native media workflows: Platforms that index media by scenes, transcripts, and tags detect chaos instantly when provenance is missing. See active updates to Azure AI Video Indexer’s feature set in release notes.
- Agentic flows need trust: Autopilot shopping assistants and answer surfaces require verifiable claims and rights, not just strong copy.
- Explainability keeps rising: Strategy tools, analytics, and compliance layers demand receipts. If you have them, you win routing decisions more often.
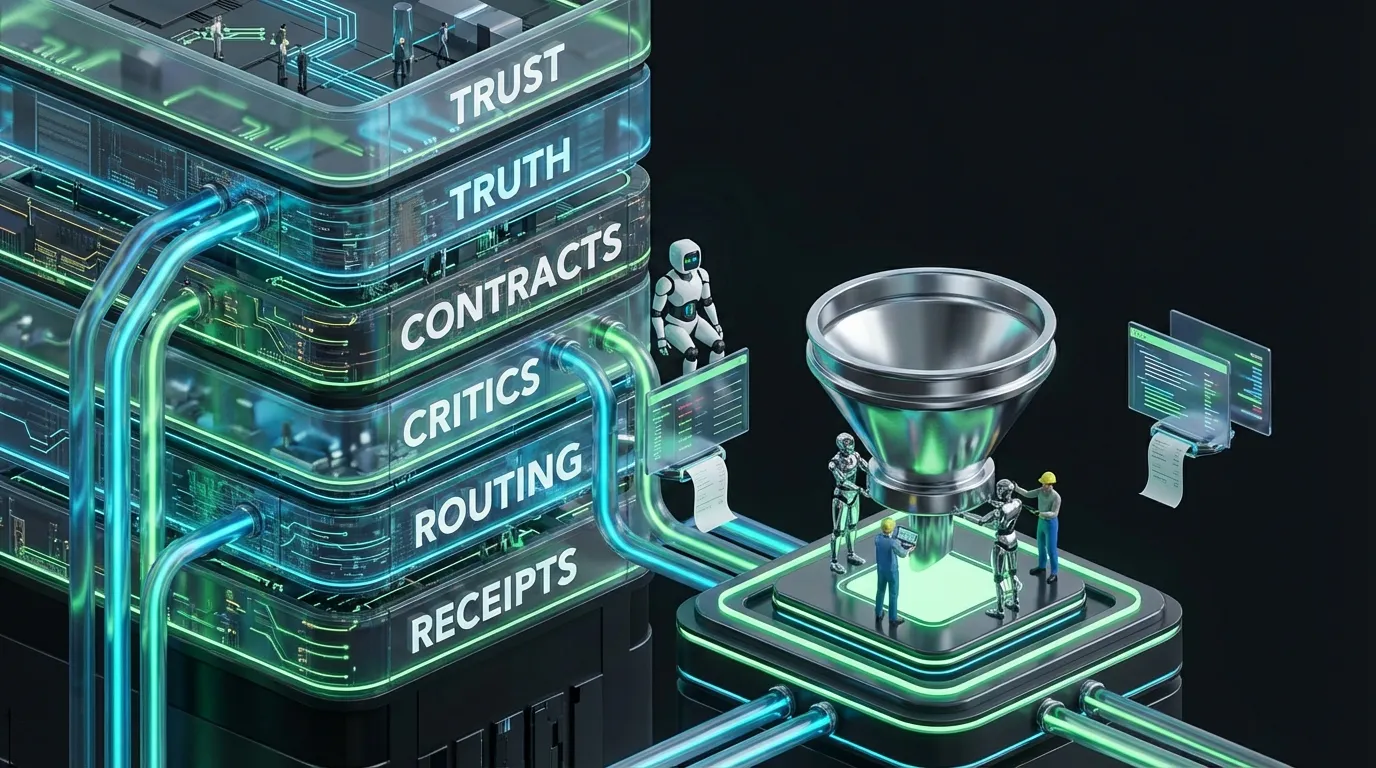
The Provenance-First Marketing Blueprint
Here is the rhythm that lets automation sprint without legal panic attacks:
[Truth]
→ product specs • pricing • eligibility • claim sources • rights • disclosures
[Plan]
→ asset schema • persona • locale • risk tier • budget caps
[Generate]
→ models draft copy, images, video using strict schemas
[Sign]
→ attach content credentials • embed watermarks • bind rights and claims
[Critic]
→ schema • claims • locale • accessibility • rights • provenance presence
[Publish]
→ channels, ads, CMS • provenance intact
[Observe]
→ inclusion • defect escapes • compliant asset cost • tamper alerts
Content Manifests: The Atomic Unit Your Stack Needs
{
"content_manifest": {
"id": "answer_card_router_v13",
"type": "answer_card",
"intent": "compare_and_buy",
"persona": "remote_worker",
"summary": "Wi‑Fi 7 router, benchmarked, verifiable claims.",
"claims": [
{"text": "1200 Mbps average on 1 Gbps fiber", "source_id": "lab_throughput_2025"},
{"text": "60 hour average setup", "source_id": "ops_sla_q4"}
],
"eligibility": {"regions": ["US-CA", "US-TX"], "sku": ["router_ultra_7"]},
"rights": {"media": ["ads", "web"], "territories": ["US"], "end": "2027-06-30"},
"disclosures": ["Sponsored partnership"],
"design_tokens": {"palette": "brand_cool", "min_contrast": 4.5}
}
}
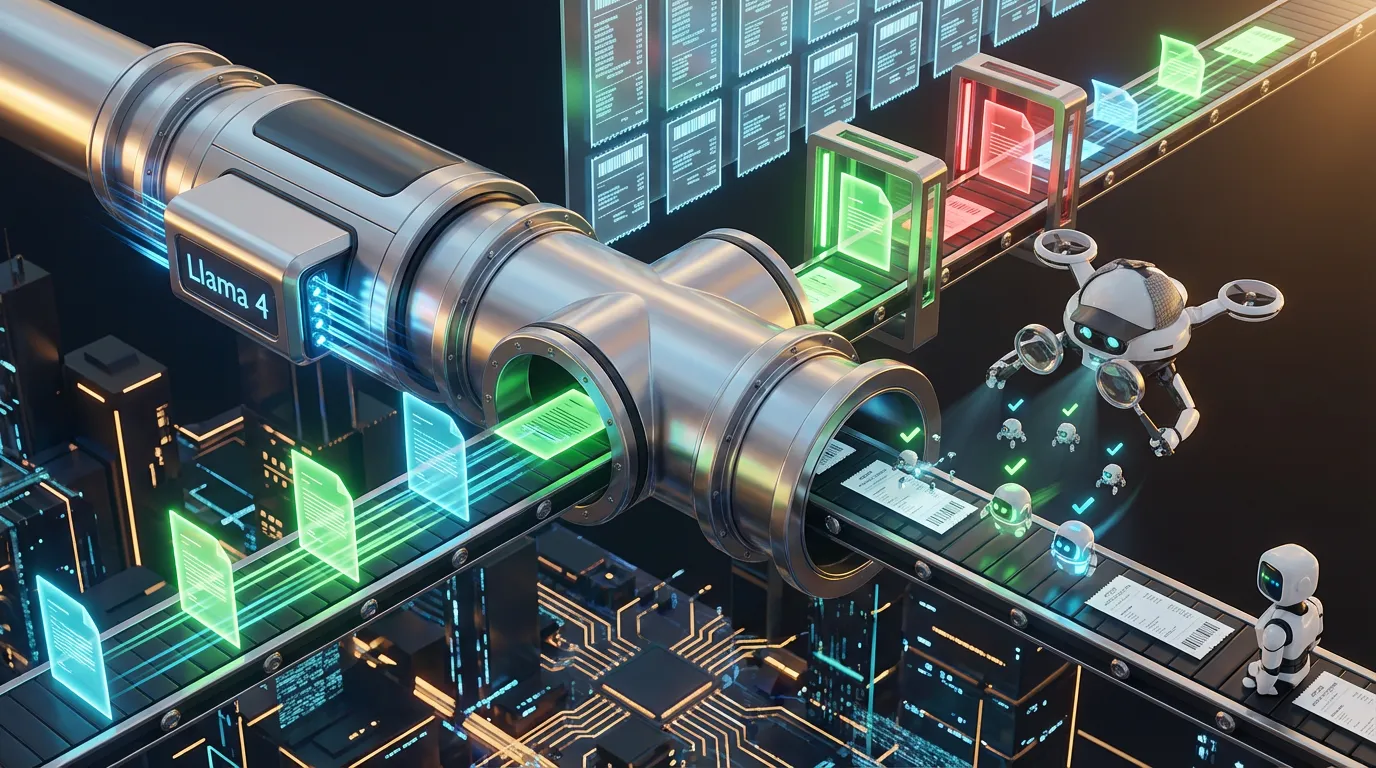
Signing and Watermarking: Bind Proof to Every Asset
{
"sign_and_mark": {
"credential": {
"issuer": "brand_signer_v4",
"assertions": [
{"action": "generated", "by": "llama_4_small"},
{"action": "edited", "by": "editor_casey"},
{"action": "claims_verified", "by": "claims_critic_v6"}
],
"signature": "<detached_sig_base64>"
},
"watermark": {"profile": "resilient_v3", "strength": 0.9, "payload": "content_manifest.id"}
}
}
Receipts, Or It Did Not Happen
{
"provenance_receipt": {
"asset_id": "answer_card_router_v13",
"model_route": ["llama_4_small", "claims_reasoner_v4"],
"inputs": {"tokens": 1620, "retrieval": 8},
"outputs": {"tokens": 260},
"retries": 0,
"human_minutes": 3.9,
"cost_usd": 0.82,
"critics": {
"schema": "pass",
"claims": "pass",
"locale": "pass",
"accessibility": "pass",
"rights": "pass",
"provenance": "pass"
}
}
}
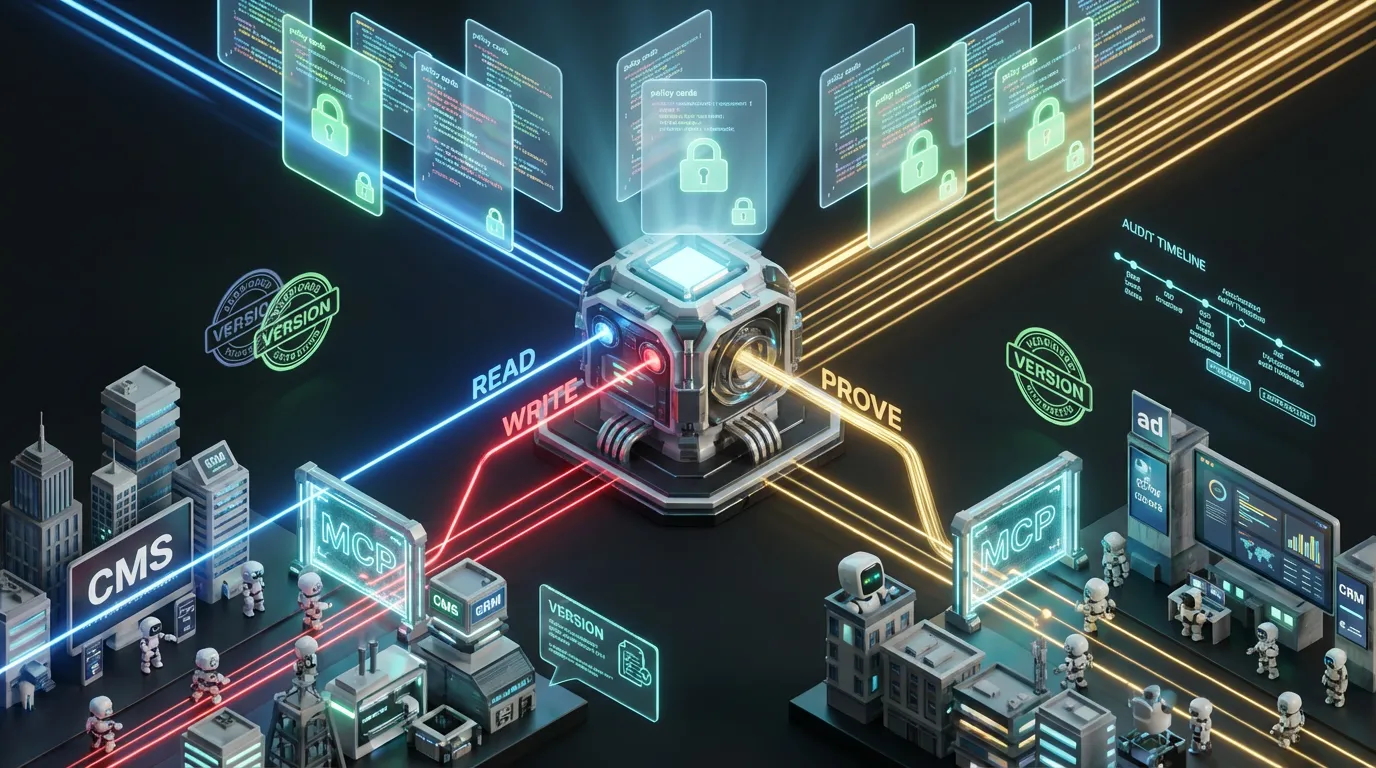
Policy as Code: Enforce Provenance or Block Publish
Slide decks will not gate busted content. Treat provenance as a go or no-go in your pipeline.
{
"policy_pack": {
"schema": {"id": "AnswerCardV13", "enforce": true},
"claims": {"numeric_require_source": true, "blocked_phrases": ["guaranteed", "number one"]},
"locale": {"currency": "auto", "date": "auto"},
"accessibility": {"alt_text": true, "contrast_min": 4.5},
"rights": {"territory_lock": true, "kill_switch": true},
"provenance": {"credential_required": true, "watermark_required": true},
"budget": {"max_cost_per_asset_usd": 1.50, "retry_limit": 1}
}
}
No-Code and Low-Code: Wire Up Without a PhD
- Leverage features in your stack: Many modern capture and edit platforms can sign and export edit histories. Turn that on and make it required in your workflows.
- Add a signing step in the middle: Insert credentialing after AI generation but before review. This reduces lost provenance if you auto-repair after critique.
- Treat manifests as first-class assets: Store manifests beside creative in your DAM or media platform. If a manifest is missing, block publish.
- Include provenance in all integrations: Every system (CMS, social, CRM) should ingest, preserve, and verify credentials and receipts. If not, add a script to repair or reattach them.
Which Proof for Which Job?
| Proof Type | Best For | Watch Out For |
|---|---|---|
| Credentials | Channel compliance, assistant preference, audit trails | Must be cryptographically bound to persist |
| Watermarking | Large-scale media verification, detecting reposts | Signal can fade with heavy editing |
| Receipts | Cost, accountability, automated regression | Pointless if bypassed pre-publish |
| Fingerprints | Deduplication, asset grouping | Not a proof of origin on their own |
Budget and Latency: Staying Fast and Cheap
Provenance does not have to slow you down or break your budget. If it does, your pipeline is mis-ordered. Avoid silent bloat with these moves:
- Batch sign low-risk assets: Single calls, separate signatures.
- Cache manifests, credentials, and prompts: Static system prompts should never burn compute twice.
- Lightweight routing first: Run quick credential and watermark checks upfront, escalate only if patterns break.
- Track time to valid: If provenance adds more than a couple of seconds per asset, reprioritize middleware order.
Failure Modes & Fast Fixes
| Failure | Why It Happens | Fast Fix |
|---|---|---|
| Credentials gone after upload | Channel strips metadata by default | Cryptographic bind plus reattach script post-upload |
| Unsupported claims sneak through | Lax or absent claims critic | Require source IDs, auto-block puffery |
| Rights violations slip | Rights live in PDFs, not in machine code | Rights as data, territory locks, kill switches |
| Watermark is too faint | Wrong strength or profile, overcompressed media | Use robust profiles, increase strength, sign post-export |
| Cost spikes from provenance | No batch signing, too many retries | Batch jobs, cap retries, escalate efficiently |
Metrics That Prove This Is Working
- Provenance coverage: Percent of shipped assets with valid credentials and watermark.
- First-pass validity: Share of assets passing all critics at generation with no human touch.
- Tamper detection rate: Pre and post-publish anomalies or stripping caught.
- Cost per compliant asset: Compute plus human minutes per asset that passes all checks.
- Inclusion rate: How often assistants and platforms pick your assets for surfacing.
- Defect escapes: Rights or claims issues per thousand assets published.
Thirty Days to a Provenance-Grade Pipeline
Week 1: Inventory and Schema
- Pick two high-velocity formats such as answer cards and video thumbs. Draft strict schemas with zero optional fields for claims, rights, and disclosures.
- Centralize truth packs (product specs, eligibility, claim sources). No source, no stat.
Week 2: Critics and Signing
- Implement critics for schema, claims, locale, rights, cost, and provenance. Fail if credentials or watermarks are missing.
- Sign assets immediately post-generation and before critic review. Store both manifest and signature next to the asset in your DAM.
Week 3: Shadow and Canary Launch
- Run a provenance-first shadow flow in parallel with business as usual. Measure time to valid, cost, inclusion, and escapes.
- Promote a canary group to publish. Reattach credentials post-upload if your channel strips them.
Week 4: Enforce and Expand
- Block all low and medium risk assets on missing provenance. Keep human review for high-risk material.
- Report provenance coverage, time to valid, tamper catches, and expand to the next highest-impact surface. For more rollout patterns, see our playbook Provenance Pipelines Supercharge AI Marketing.
How Provenance Makes AI Agents Less Chaotic
- Smarter routing: Assistants can pick cheaper and faster models when schema and provenance are strong. Escalation stays rare.
- Safer autonomy: Receipts and credentials enable kill switches and audit rollbacks on demand.
- Seamless handoffs: CMS, ad networks, and CRM systems accept rights-aware assets, so fewer Slack panics and more frictionless handoffs.
Playbooks by Team Size
Solo Creators & Micro Brands
- Stick to two schemas (video and card). Require credentials and a watermark.
- If an asset fails, run one repair. Then escalate to human approval. If credentials are missing, nothing ships. Track coverage and speed weekly.
Mid-Market Growth Teams
- Centralize claim sources and rights. Enforce through territory locks and expirations.
- Batch-sign low-risk assets, overnight if needed. Route light, cap retries, and pin cost per asset.
- Publish from your DAM to credential-friendly channels. If a channel strips, reattach after upload.
Enterprise & Regulated Markets
- Version your critics, policies, and signing agents. Hold monthly regression tests for quality, cost, and drift.
- Maintain global kill switches by asset, vendor, or model. Keep full audit trails.
- Use strict review gates for regulated content such as pricing, HR, or health claims.
Governance That Accelerates, Not Slows
- No receipts, no ship: Model routes, sources, signatures, and reviewers are logged, always.
- Code enforces policy: PDFs never stopped a compliance fail. Critics and code do. Treat it as stop-the-line, not hope-it-is-fine.
- Humans set taste and risk boundaries: Agents generate, critics gate, editors own the final cut. Keep the hybrid system by design.
The COEY Take
Provenance is your marketing unlock. It is not just a checkbox for regulators. It is how you make every bot, channel, and dashboard pick you first. When every asset is signed, rights-aware, and natively structured, you move faster, publish smarter, and never waste a minute arguing in Slack. Automate proof, route small first, attach cryptographic receipts. Save real humans for judgment, novelty, and the edge cases that matter.