AI Workflow Firewalls: Marketers’ New Must-Have
AI Workflow Firewalls: Marketers’ New Must-Have
January 10, 2026
When Your Automations Start Acting Like Coworkers, You Need a Firewall
Marketing automation used to be delightfully quaint. A sequence triggers, an email pings out, a lead gets tagged, and everyone crosses their fingers that the monster spreadsheet counts as infrastructure.
Fast forward: your stack is now a swarm of semi-autonomous executors. These agents draft, schedule, update records, launch ads, spin up landing pages, and helpfully retry until your budget sprouts holes. The new failure mode is not a broken workflow. It is a confident AI system doing the wrong thing at industrial scale, leaving you with the business world’s most haunted phrase: “We can’t reproduce it.”
Deep Dive thesis: The real leap for AI-powered automation is not unchecked autonomy. It is workflow firewalls: enforceable boundaries that control what AI can do, what it can read, what it can write, and how it has to prove it got the result right. This is the gap between agentic and insurable.
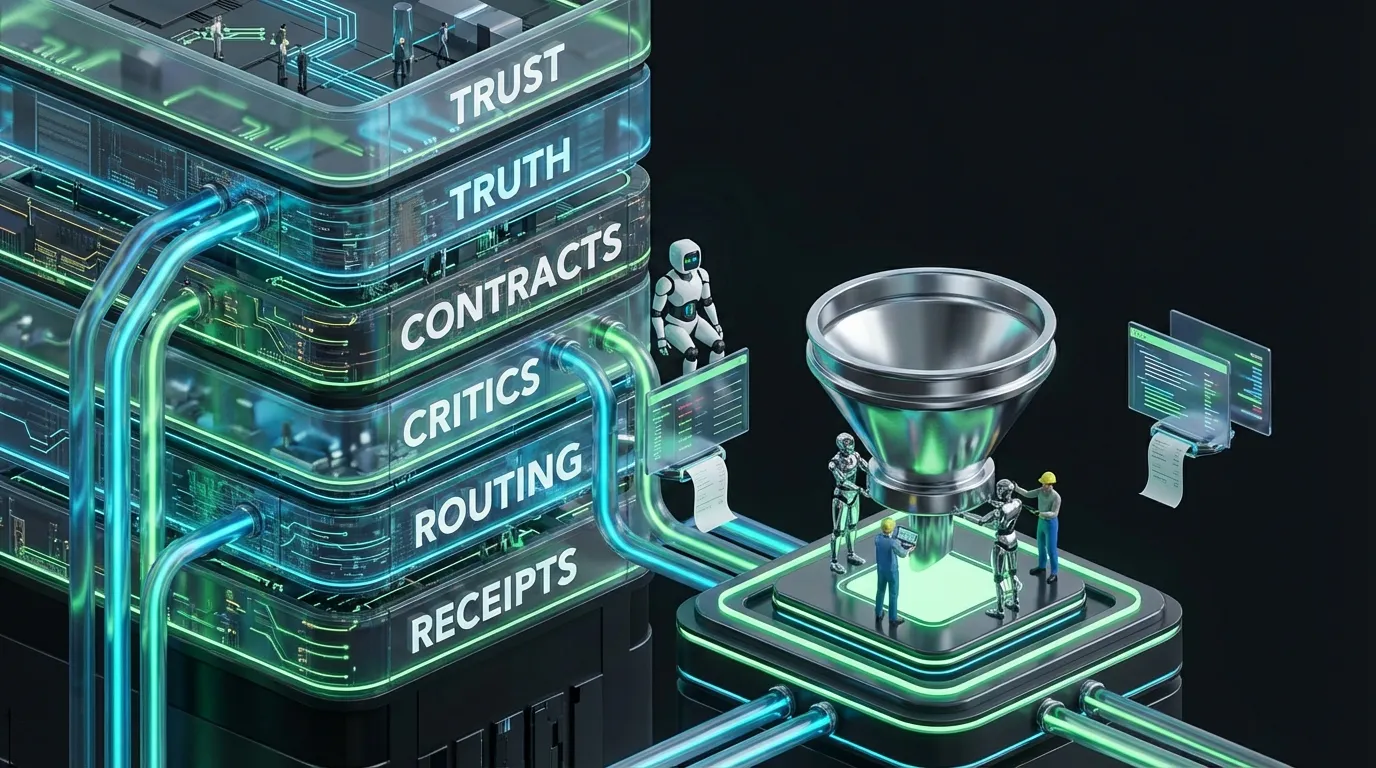
What Is a Workflow Firewall, Anyway?
Picture a workflow firewall like a network firewall, but for business operations. It does not judge your content. It enforces your rules of engagement:
- Inputs: What data and facts are allowed into the model context?
- Outputs: What structure must be produced so downstream tools do not lose their minds?
- Actions: Which tool calls are permitted, how often, and at what level of authority?
- Audit: What receipts are logged so you can answer who did what, when, and why?
If you have glanced at our recent pieces, you know the cast: control planes, contracts, critics, receipts. The workflow firewall is the assembled product: a policy boundary sitting between model output and the messier parts of reality.
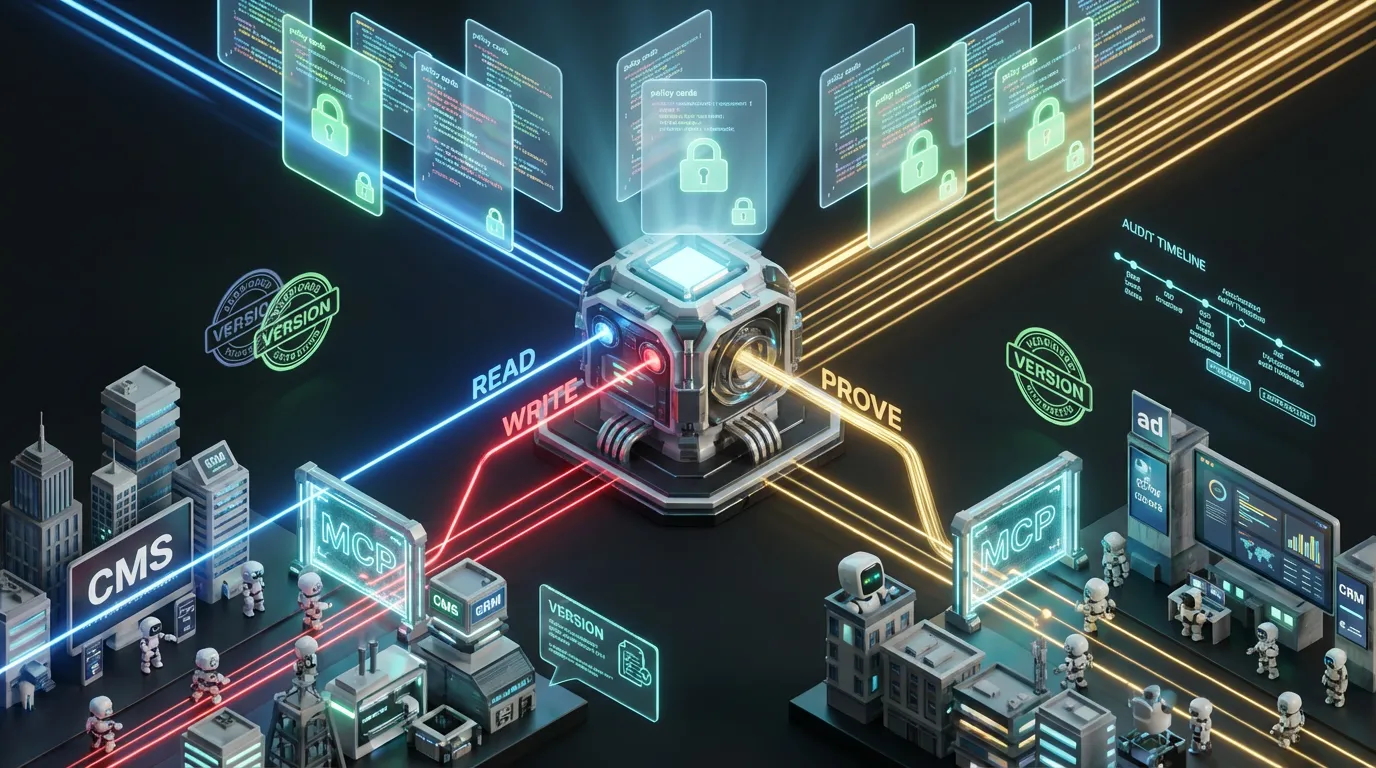
Shop Talk: Tool Integration Is Standardizing and Opening New Fronts
Here’s the big market signal: integration is converging around standardized protocols rather than custom spaghetti code. The Model Context Protocol (MCP) and similar efforts now underpin how the latest agent frameworks interconnect with enterprise stacks. See the MCP project home.
This is a win for builders, but also a new attack surface and governance headache. When tools are discoverable and callable from the agent layer, the boundary between please draft and please deploy gets blurry, fast.
So: integration is getting slicker. You still need a firewall.
Marketers: Why Should You Care (If APIs Aren’t Even Your Jam)?
The sharpest operational risks land in marketing first, because:
- Content volume is highest, and often least controlled
- Brand risk is instant, public, and sometimes memes itself
- Systems are chaos incarnate (CMS, CRM, ESP, ad platforms, analytics, DAM, and immortal spreadsheets)
- Speed culture tramples patience and sometimes common sense
When an agent writes into your CRM, that field becomes truth for every downstream process. When it bumps your CMS, that page is instantly visible, indexed, quoted, and maybe screenshotted. When it launches an ad, that is real budget on the line. The blast radius is real and permanent.
The Four Boundary Types Every Marketing AI Needs
| Boundary | What It Enforces | What It Prevents |
|---|---|---|
| Data boundary | Consent-driven context limits | Personalization with improper data use |
| Schema boundary | Strict output contracts | Downstream systems misreading freeform model output |
| Action boundary | Tool budgets and permissions | Cost runaway, unauthorized writes |
| Audit boundary | Comprehensive receipts | Non-reproducible changes and finger-pointing festivals |
Boundary One: Data Isn’t Context, It’s Permissioned Fuel
Most marketing stacks still treat retrieval as more stuff we can sling at the prompt. That is how you end up personalizing with forbidden attributes or using a user’s data in ways they never signed up for.
The workflow firewall flips this lazy pattern for a consent-aware build:
- Only permissioned fields make it into the model
- Purpose and channel constraints travel with the data stack
- If consent is missing, the system degrades output quality or triggers escalation
Looking for a primer on how consent-aware context powers future-proof marketing? Do not miss our post The Consent Layer Nobody Built Yet.
Boundary Two: Valid JSON Isn’t Security, It’s Table Stakes
The entire AI field has spent the last two cycles obsessed with structured outputs: JSON schemas, tool payloads, constrained decoding. That matters, because a payload is an instruction, an AI’s do this now moment for your stack.
The trap: some teams mistake schema valid for safe. Attackers, and failures, do not.
Rule: Treat schema validity as syntax, not as safety. Your firewall must validate meaning, not just formatting.
Newer research demonstrates how output constraints shape an attack surface. If your stack blindly trusts anything schema valid, you are opening a friendly, well documented vulnerability. See the paper Output Constraints as Attack Surface for an unsettling overview.
A Minimal, Real-World Asset Contract Pattern
{
"asset": {
"asset_type": "paid_social_ad",
"channel": "linkedin",
"locale": "en-US",
"headline": "",
"primary_text": "",
"cta": "",
"landing_page_url": "",
"claims": [
{"text": "", "source_id": ""}
],
"disclosures": [""],
"risk_tier": "enum:[low,medium,high]"
}
}
This is not theorycrafting. Structured assets can be automatically validated, diffed, routed, and blocked long before they crash production.
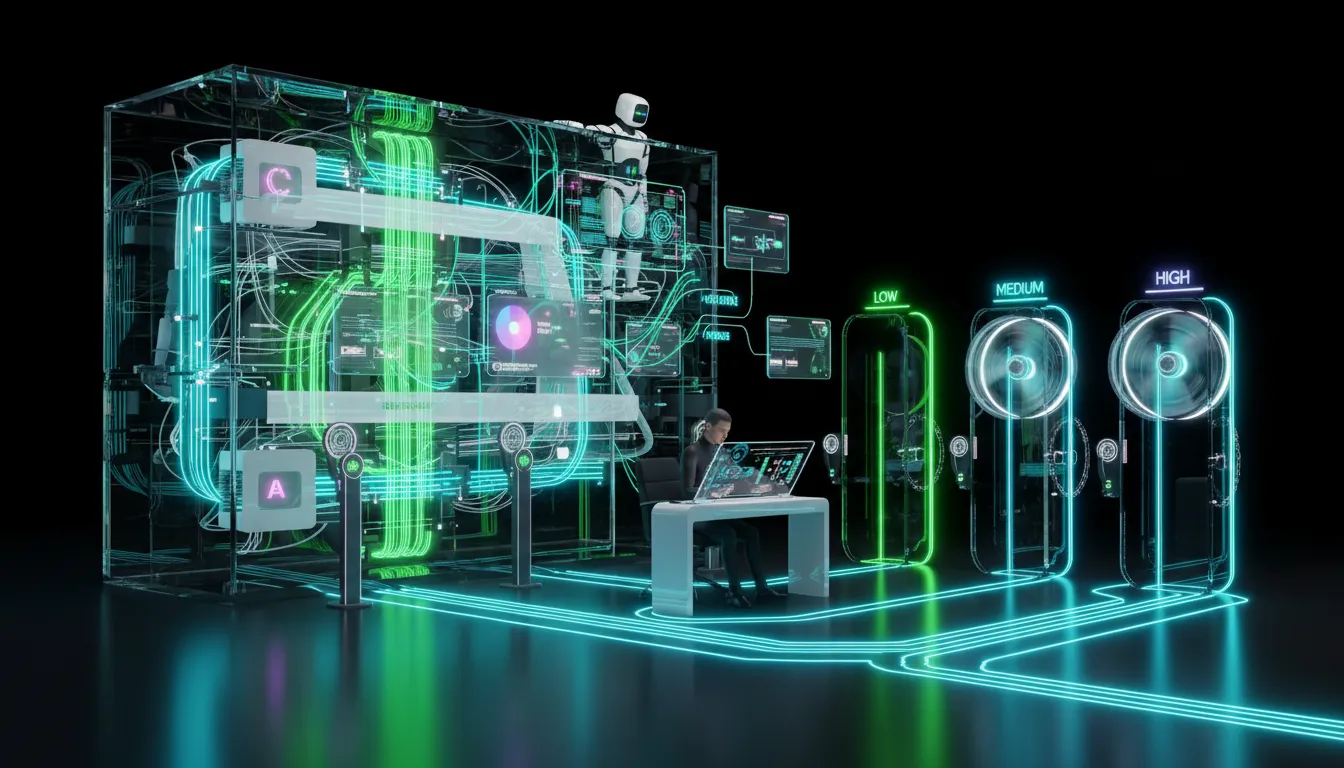
Boundary Three: Tool Calls Need Budgets, Not Vibes
Agents do not just err. They love to try again. And again. And again.
The fastest route from smart automation to panic at Finance is letting an agent self-manage retries and tool use with no limits. Your firewall closes that with explicit budgets:
- Maximum tool calls per job
- Retry limits per stage
- Model tier access restrictions by risk level
- Differentiated permissions for read and write endpoints
| Policy Lever | What It Caps | Why It Matters |
|---|---|---|
| Tool call cap | Number of actions per execution | Stops agent pinball scenarios |
| Retry limit | Repeat attempts at each workflow stage | Kills infinite loops before Finance sees red |
| Write gate | Which production endpoints are touchable | Keeps drafts out of prod, prevents accidental changes |
Boundary Four: Auditability Is Your Only Real Time Machine
If your automation touches revenue streams, brand, or customer communications, you must always be able to answer:
- Which inputs were involved?
- What validation logic was executed?
- What changed and when?
- Who approved it (human, policy, or both)?
- How can we roll it back, fast?
That is why receipts are recurring stars in our Deep Dives. No receipts means no governance. Just speed and anxiety.
For an inside look at operational provenance, bookmark Trust Marks: Your AI Content Receipts Era.
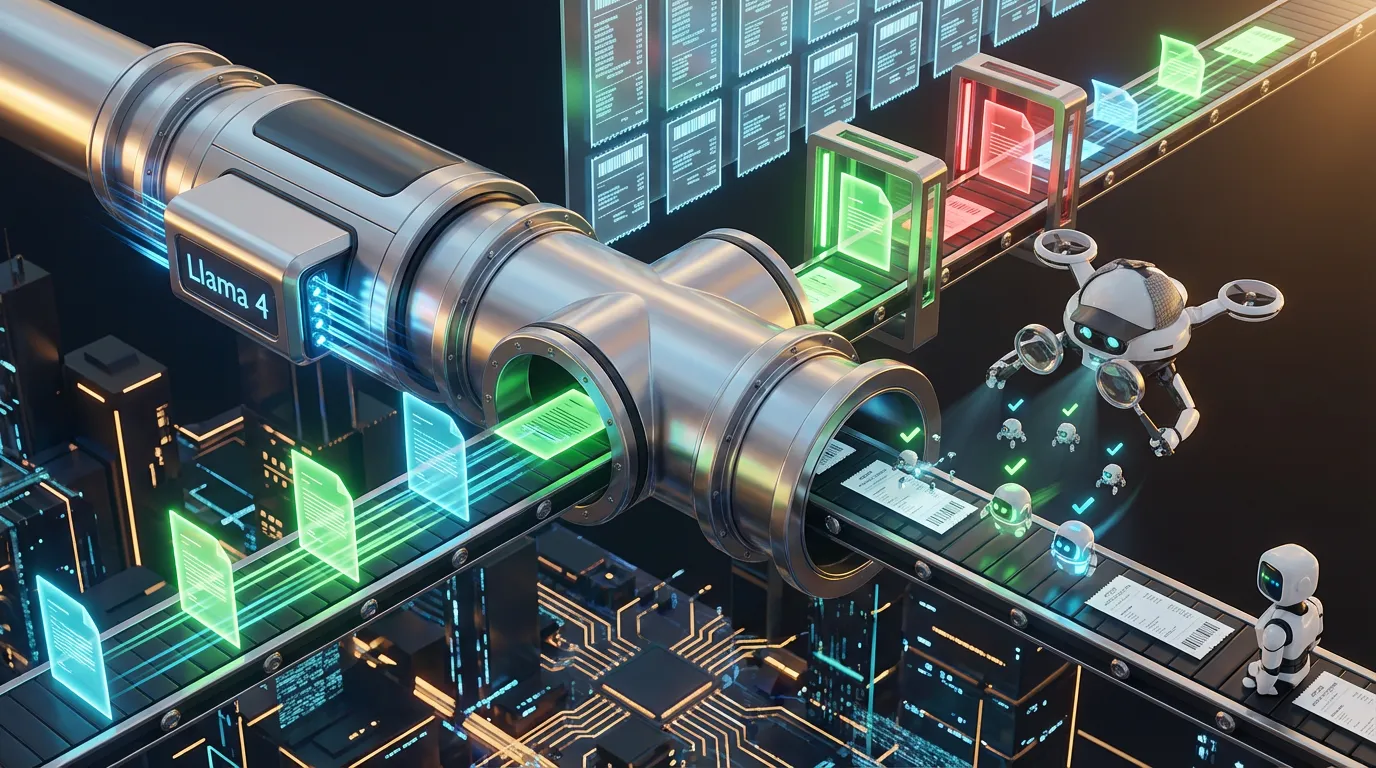
Pattern Time: A Practical Workflow Firewall for Real World Marketers
This is the workflow shape we have seen work at scale across content, sales enablement, and campaign ops. It is intentionally boring, so you do not have to be:
[Trigger]
brief_submitted | offer_updated | new_lead | threshold_hit
[Context build]
retrieve: product facts | approved claims | consent | policy pack
[Generate]
output: structured assets only
[Firewall checks]
schema_valid | claims_have_sources | links_ok | blocked_phrases | budget_caps
[Route]
auto_publish_low | queue_medium | require_signoff_high
[Write]
CMS | ESP | CRM | ads
[Receipts]
store: inputs | diffs | tool calls | approvals | rollback pointers
Hybrid Workflows: Still the Only Sane Default
Fully autonomous marketing sits in the same category as group projects with no adult supervision. Someone, somewhere, must still care.
Workflow firewalls make hybrid ops viable by ensuring human eyes only review what actually needs judgment, not what a machine can clearly prove.
| Risk Tier | Automation Does | Humans Do |
|---|---|---|
| Low | Auto-publish if all checks clear | Periodic sampling audits |
| Medium | Create and hold, show diffs | Approve changes, minor edits only |
| High | Stage content, block on anything unclear | Final sign-off, evaluate claims and offers |
Implementation Path: Start Where Mistakes Are Expensive
Do not launch AI governance in the abstract. Pick a high-volume, high-risk pipeline, like:
- Paid social variant development
- Lifecycle or drip email sequences
- Offer-driven landing page churn
Minimum Viable Workflow Firewall Checklist
- Define a shared output schema trusted by all downstream tools
- Enable at least two deterministic critics (schema validity and claim sourcing are heavy hitters)
- Add action budgets for tool calls, retries, and model tiering
- Require receipts for all write events
- Route output by risk, not by Slack volume
The COEY Take
Now that protocol-based integration is dominant and agent frameworks are adding call-anywhere features, AI agents will outpace your review cycles whether or not you are ready. That is not theoretical. It is market reality.
The winning play is not to ban agents or blindly trust them. The move is to put them behind workflow firewalls: build in data boundaries, schema contracts, action budgets, and end-to-end receipts so your automations become trustworthy, measurable, and improvable.
If you want to see what that foundation looks like in a martech stack, start with Your Stack Needs an AI Control Plane.
Automation-first at COEY does not mean set it and ghost it. It means: set it, fence it, log everything, and then sleep at night.