Build Your AI Content Provenance Layer Fast
Build Your AI Content Provenance Layer Fast
October 27, 2025
Trust at Scale Is a Pipeline Problem
Generative AI did not just fulfill marketers’ wildest content dreams; it also created a trust deficit the size of the Web3 hype crater. Customers scroll and wonder, “Is any of this real?” Platforms keep tightening rules and rating signals that favor verified origins. Legal reviews every QA doc like it might turn into a regulatory drama. The fix is not fewer robots. The fix is a provenance layer that travels with every asset, from prompt to publish, proving what it is, how it was built, and which rules it followed. Authenticity is not a press release. It should be baked into your production stack, surfaced for every stakeholder, human or bot.
Metadata is your new brand voice. Content Credentials are now shipping in real tools. For a marketing playbook, see our deep dive on Content Credentials as a growth lever.
Why Provenance Just Jumped to the C-Suite
Three structural shifts made provenance everyone’s business, not just an AI side project:
- AI turned content into a commodity. Infinite outputs, so credibility and traceability become the signal.
- Platforms reward transparency by design. Major platforms now label AI involvement in ads and media. One example is Meta’s policy for ad transparency on generative AI content (details).
- Enterprise automation is real and regulated. Brands delegate more work to agents and then need receipts. Lineage, policy, and one-click rollback are now board-level asks.
Your content pipeline is now a governance surface. Provenance is risk management, distribution insurance, and a KPI the CMO can track.
The Stack Evolves: What’s New for 2025
The tools to implement production-grade authenticity have matured quickly. What matters now:
- Content credentials are native, not bolt-ons. Many creative tools, cameras, and document editors ship with C2PA-conformant features built in.
- Watermarking is multimodal and model-aware. New methods add invisible signals to images, audio, video, and even text. Google’s SynthID provides detection and text watermark options (overview).
- Agent frameworks track everything. Off-the-shelf frameworks can append prompts, source logs, and lineage metadata by default.
Perfection is not the bar. “Defensible and automatable” is. The new stack is better than vibes, fast enough for your pipeline, and priced for growth.
The Provenance Stack for Modern Marketing Workflows
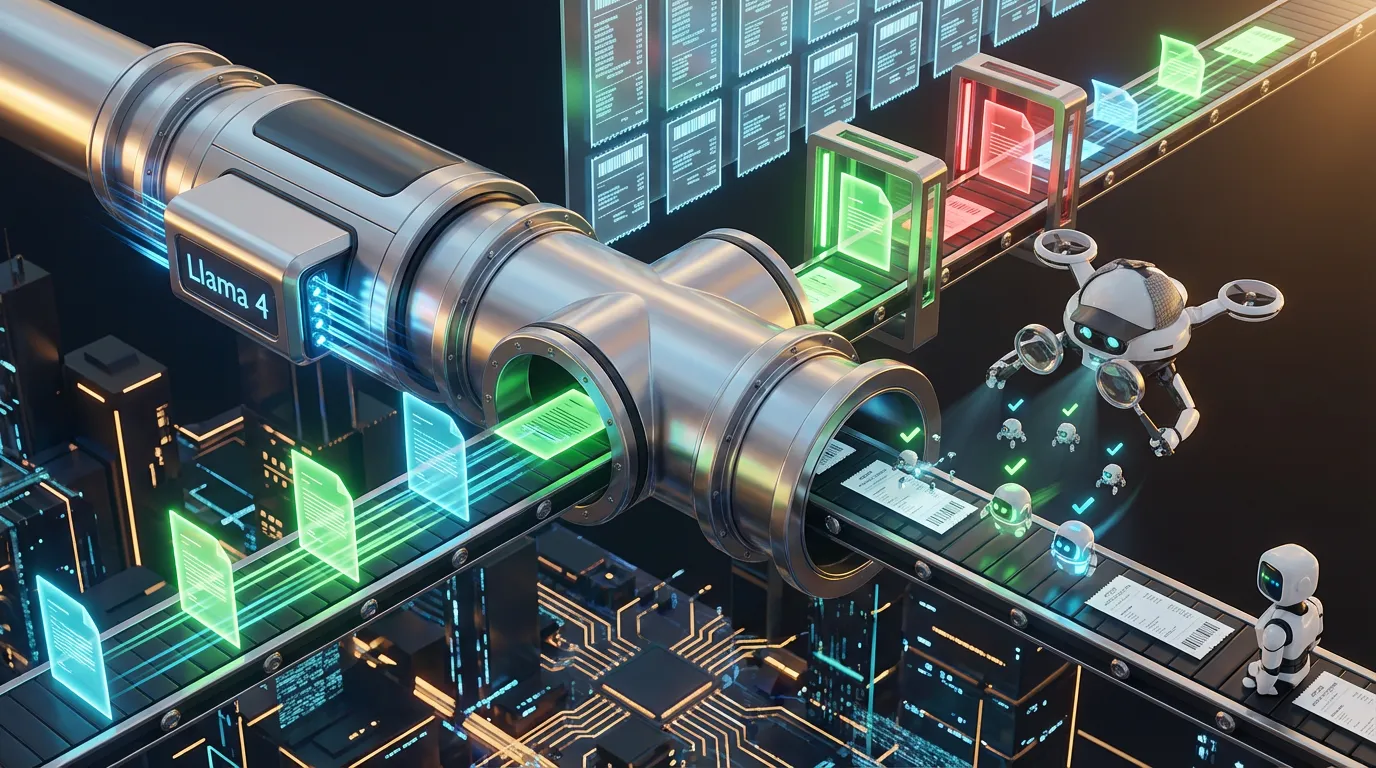
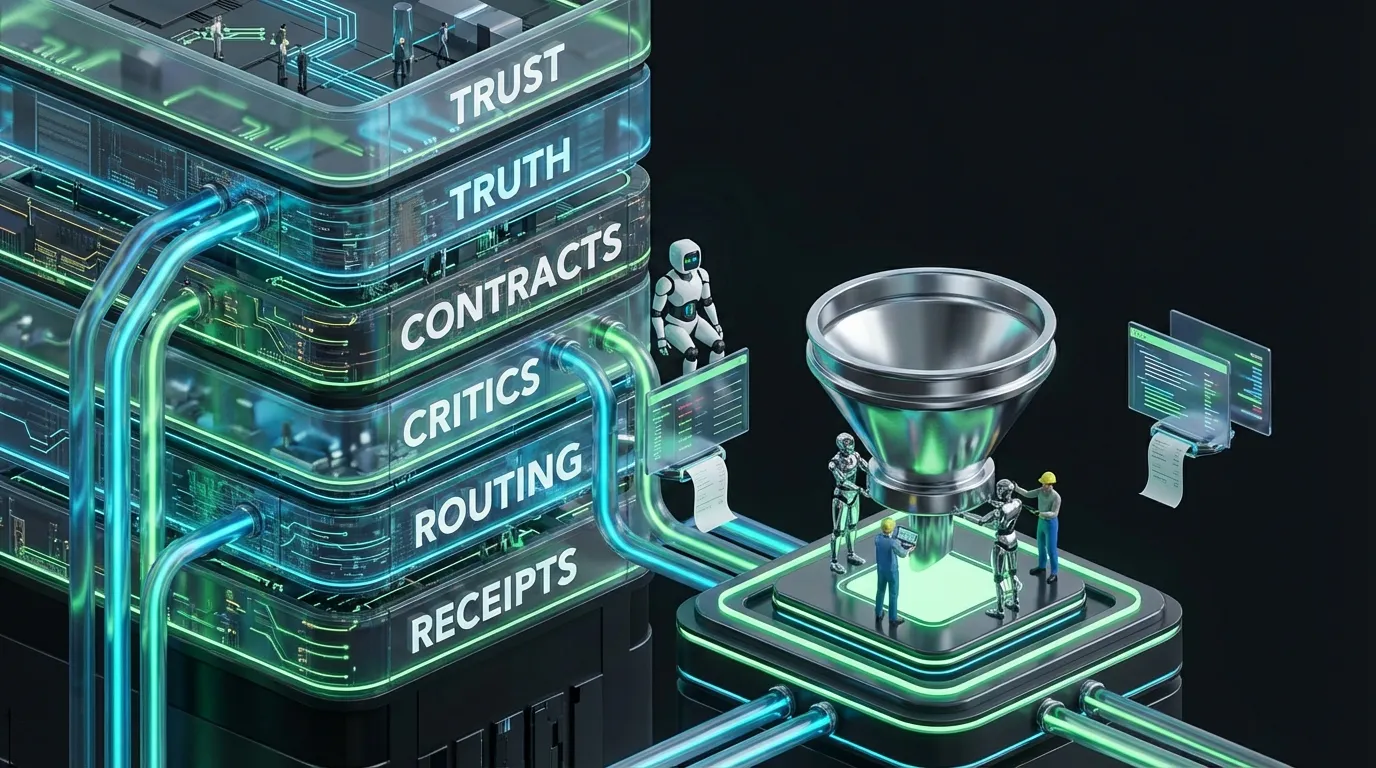
Think of provenance as the invisible backbone under your content supply chain. It captures signals at every stage: creation, validation, recording, exposure, and verification.
- Create: Log prompts, model version, and sources at generation. For AI media, embed watermarks or credentials during render.
- Validate: Automated critics scan claims, citations, and tone. Block assets that miss the mark.
- Record: Each asset gets a manifest with lineage, reviewers, and cryptographic hashes.
- Expose: Show human-readable disclosures and machine-readable credentials to maximize platform trust and reach.
- Verify: At serve or ingestion, confirm credentials, validate watermarks, and log any policy deltas.
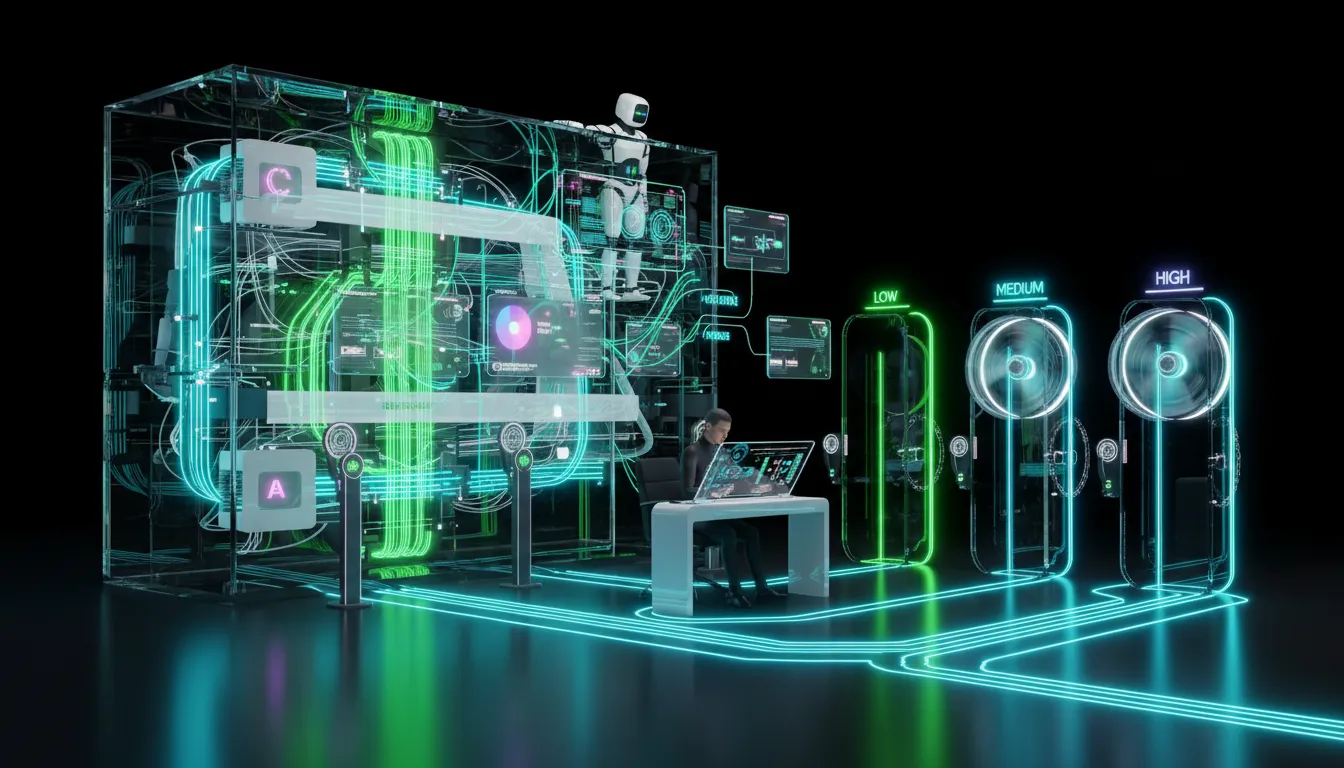
Policy as Code: Or It Didn’t Happen
A provenance policy written in a PDF is still a rumor. Code it, or your automation will not care.
{
"provenance": {
"require_credentials": true,
"watermark": {
"enabled": true,
"modalities": ["image", "video", "audio", "text"]
},
"log": {
"capture": ["prompt", "model_id", "tool_calls", "sources"],
"store": {
"location": "dam",
"format": "json",
"retention_days": 365
}
},
"claims": {
"require_source": true,
"allowed_sources": ["docs", "pricing", "case_studies"],
"blocked_phrases": ["guaranteed", "fastest ever"]
},
"approvals": {
"low_risk": {"autopublish": true},
"medium_risk": {"reviewer": "editor"},
"high_risk": {"reviewers": ["legal", "brand"]}
}
}
}This is the DNA of defensible, automatable provenance. Layer it into orchestration. No PDF, no exceptions.
Watermarks vs Credentials vs Fingerprints: The 2025 Reality
| Technique | Works For | Strengths | Limitations | Use It When |
|---|---|---|---|---|
| Content credentials | Images, video, audio, docs | Cryptographically signed, edit history, tamper-evident | Needs tool support at generation or edit | Audit-grade lineage in a controlled toolchain |
| Invisible watermarking | Images, video, audio, and sometimes text | Survives edits, scalable detection | Dependent on model and method, not legal proof | Fast authenticity sweeps at scale |
| Content fingerprinting | Any file, hashed or perceptual | Simple, dedupe and tracking, quick | Fragile to major edits, not human-readable | Ops, versioning, or duplication control |
| Plain-language disclosure | Any distribution channel | Audience clarity, meets platform norms | Honesty required, machine-readability optional | User-facing transparency or compliance |
Best practice: Layer your approach. Use credentials at source, watermarks at distribution, fingerprints for ops, and human-readable disclosure everywhere.
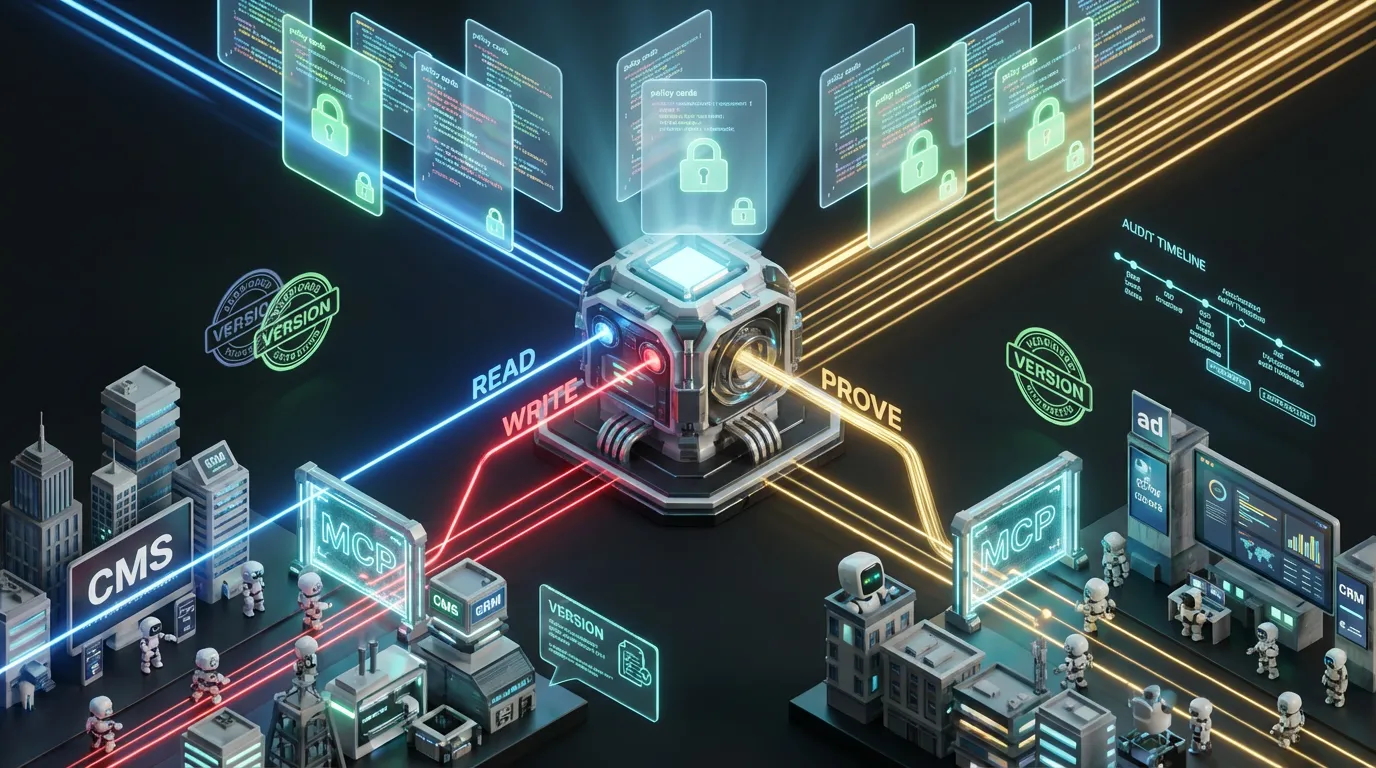
Provenance in Action: From Watermark to Workflow
Provenance is not a sticker you add just before publish. It is a set of automated and human-in-the-loop steps woven into existing processes:
- Prompt and plan: Agents draft briefs, cite sources, and cache context. Log every prompt and model ID.
- Draft: Lightweight models generate. Frontier models polish. Lineage logs by default.
- Critic and claims check: Evaluators enforce schema and source requirements. Fail compliance and block publish.
- Render and stamp: Exports embed credentials and apply watermarks. Write a manifest to the DAM in parallel.
- Publish and verify: The CMS validates credentials, attaches disclosures, and logs state and reviewer ID.
- Monitor and roll back: Find any out-of-policy asset by manifest and unpublish or update in one click.
Provenance Manifest Example
{
"asset_id": "ad_0427_en_us_yt_15s",
"created_at": "ISO-8601",
"lineage": {
"prompt_id": "p_9a7f",
"model": "frontier_text_vX.Y",
"tools": ["retrieval:v2", "brand_critic:v4"],
"sources": [
{"id": "pricing_2024q4", "hash": "sha256:..."},
{"id": "case_study_acme", "hash": "sha256:..."}
]
},
"policy": {
"claims_checked": true,
"blocked_phrases": [],
"risk": "medium",
"approvals": [
{"role": "editor", "user": "jkim"}
]
},
"credentials": {
"embedded": true,
"signature": "cms-signer-01"
},
"watermark": {"image": true, "audio": true},
"hashes": {"file": "sha256:...", "frames": ["..."]}
}Boring, consistent, automatable. Boring scales, which is what you want.